Curious about cybersecurity?
Cybersecurity in Context introduces cybersecurity to undergraduate students and for self-study
The book uses a new approach to teaching cyber—Cybersecurity in Context supports a three or four-credit course with a technical lab
Cyber is a technical field. You can learn technical skills and have a rewarding career in cybersecurity
Chapter 1 and the Table of Contents are here.
Order Now
Cybersecurity in Context introduces students to the most important themes that envelop the field
Everyone now has a stake in the healthy functioning of computer communications and control networks, in the devices and services dependent on these networks, and by implication, in all of the complicated infrastructure required to keep networks, devices, and services operating.
Cybersecurity in Context explains how cybersecurity has come to encompass these interests, how cybersecurity is conceptualized, and how cybersecurity concerns and rules permeate the public and private sectors.
Written for introductory cybersecurity courses, Cybersecurity in Context outlines the most important forces that have come to shape cybersecurity—from macro-level concerns, such as the security of the state and the operation of an innovative private sector, to micro-level concerns and individual decision-making.
Cybersecurity in Context explains internet technology with hands-on exercises showing how the internet is vulnerable and why software and hardware exploits stubbornly persist.
Comprehensive treatment of the epistêmê and technê of cyber
What the experts say…
A comprehensive, multidisciplinary introduction to the technology and policy of cybersecurity. Start here if you are looking for an entry point to cyber
Bruce Schneier, Author of A Hacker’s Mind: How the Powerful Bend Society’s Rules, and How to Bend them Back.
…“Cybersecurity in Context” fills a long-standing gap. It does not tell readers what to think—it teaches them how to think about cybersecurity in a connected, contested and continually evolving world. For that reason, it deserves a place in the Cybersecurity Canon Hall of Fame.
Josiah Dykstra, Trail of Bits
Cybersecurity is as important as it is exciting
Cybersecurity experts protect the associational, free speech, and privacy rights necessary for a free society
Students—Imagine a future you… Working in cyber, you…
- Analyze whether a series of posts on social media are the product of authentic user activity or part of a coordinated attempt to influence understanding of a political issue
- Help a client investigate a security incident to determine its severity
- Inspect a suspicious software package that was emailed to your COO. Within the software, you find that malicious code seeks to steal valuable trade secrets from your company
- Examine the logs of recent voter registration changes at the Secretary of State’s office. You learn that someone has systematically changed the registration records of voters from poor neighborhoods around the state
- Test a network to determine whether an adversary can access devices on the network and take them over
Cybersecurity in Context includes a full set of resources for teachers
We reject “find the answer” teaching. Our formative evaluation exercises offer the student the opportunity to develop their own arguments and insights.
The book comes with:
- A collection of technical exercises with a companion VM
- A full set of slides, refined over years, keyed to each chapter of the book
- The book has over 120 discussion prompts, and sample discussion points are in the teachers manual
- Each chapter has at least one significant assignment, designed for individual or group projects—there are 30 exercises in the book
- The teachers manual is over 100 pages long and it actually useful. It proposes different assignments and ways to teach the course.
- A model syllabus
- Two chapters teaching policy analysis and scenario planning
- The course can be taught with an exam, or with a projects-based focus
The book focuses on the key wrapping elements of cybersecurity: Frameworks, not this week’s security breach. Think economics, psychology, military science, IR theory, and law
Committed to inclusion
Anyone—including you—can learn the skills necessary for success in cyber
Do not be intimidated by technology! Technological skills—like all skills—can be learned. Cybersecurity in Context sets students on the path to learning the technology of cybersecurity with hands-on labs. There are no prerequisites.
Cybersecurity leadership requires many non-technical skills as well, ranging from management to analysis to policy evaluation and implementation. The most successful people in cybersecurity blend technical prowess, soft skills, and policy context. This is why Cybersecurity in Context connects the dots among theory, law, and policy implementation of cybersecurity rules.
You can do well while doing good in cybersecurity. According to the US Bureau of Labor Statistics, the median pay for information security analysts (an entry level position) is just over $110,000. Highly-skilled candidates may make several times this much, or more. And even better: the U.S. government predicts the field will grow more than 30% in the next decade. Positions are available across the nation.
There is a career for you in cybersecurity.
Why is cybersecurity in context important?
Context is necessary for cybersecurity because people trained in different fields may have different assumptions. To some, the field is purely technical, and adherents of this view may see policy as irrelevant or adjacent to code-based approaches. Lawyers might apply a crime or law of war frame to their analyses, and thus overlook important technical or political developments. Political scientists may take the state as the unit of analysis, leaving individuals and companies’ concerns without remedy.
Cybersecurity leaders need to be able to recognize the different contexts of cybersecurity in order to be effective.
Security context has a second meaning as well: the ability to critically analyze security as a social phenomenon. We must be able to recognize who pays and who benefits from calls for increased security.
A multidisciplinary approach
The Labs
Cybersecurity in Context comes with straightforward labs that could be assigned as homework or used to support a 1-credit in-class lab. The website has a special virtual machine we have prepared that has all the tools and data necessary. We recommend that all students do the Introduction to Linux first. But after that lab, one could teach them in any order. The order we have below roughly follows themes of the book.
Meet the Authors
Golden G. Richard III
- Professor of Computer Science and Engineering at Louisiana State University
- Director of the LSU Cyber Center and Applied Cybersecurity Lab
- Associate Director for Cybersecurity, Center for Computation and Technology (CCT)
- Fellow of the American Academy of Forensic Sciences
- Over 40 years of experience in computer systems and security

Chris Jay Hoofnagle
- Professor of Law in Residence at University of California, Berkeley
- Affiliated faculty, Simons Institute for the Theory of Computing, Center for Security in Politics
- Author of The Quantum Age (with Simson Garfinkel, Cambridge Univ. Press 2022) and FTC Privacy Law & Policy (Cambridge Univ. Press 2016)
- Of Counsel to Gunderson Dettmer, LLP
- Serves on boards for Constella Intelligence and Palantir Technologies


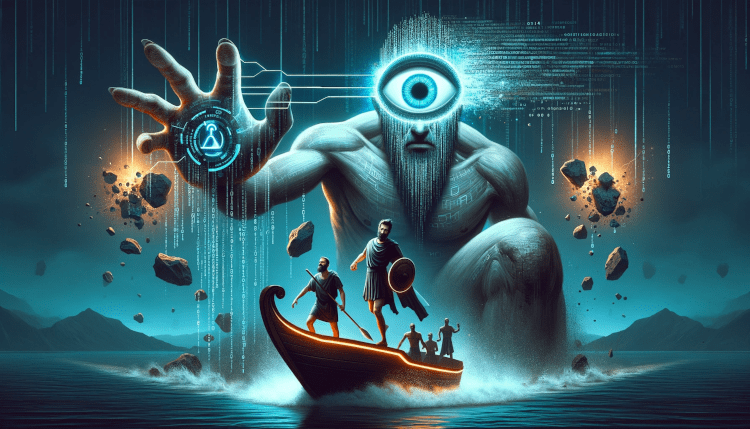
The Hero and Cybersecurity in Context
We decorated Cybersecurity in Context with allegories from the Iliad and Odyssey. Why?
Recall from the story that Odysseus convinces Polyphemus that his name is “Noman.” Odysseus intoxicates Polyphemus with wine while his soldiers sharpen a stake and use it to blind the giant once he loses consciousness. Polyphemus calls for help, but falls for the trick of telling his friends “Noman is killing me,” and thus the rescuers leave confused. Once Odysseus is on the escape, he announces his true identity to Polyphemus.
Conflicts in cybersecurity often have similar dynamics—anonymity, the tricking of a victim into creating a vulnerability, rapid action that serves the attacker’s goal, misleading the victim about the identity of the attacker, sometimes attribution of the true identities of attackers, along with many avenues of pursuit against the wrongdoer.
As you consider the allegory, know that thinkers in cybersecurity are not certain whether cyberattacks are most like the deception surrounding Odysseus’ name, the wine, or the stake. As cybersecurity evolves, it may take the form of one or all three of these elements.
Cyber and Mētis
The Iliad and Odyssey are infused with the Greek concept of Mētis. Mētis, the Greek Titan mother of Athena, represented wisdom and cunning.
Mētis presents a dilemma: we are ambivalent about tricks and tricksters. On one hand, we admire tricksters. Yet on the other, tricksters can wreak havoc. Homer put the clever and their tricks at the center of the story—Penelope’s loom, Athena’s disguise as Mentor, Patroclus’ donning of Achilles’ armor, Helen’s perfidies, and Odysseus’ too-many-to-enumerate schemes.
The tricks in the Odyssey and Iliad are relevant to today’s cybersecurity conflicts. Cyber creates new opportunities for ingenious cunning and for a new generation of heroes
Emily Wilson, in her translation of the Odyssey, opens the work by describing Odysseus as “complicated.” And so are our feelings about the modern tricks so frequently used in cybersecurity.
Updates and news
-
Documents for CiC
Our documents page has updates and teaching materials for CiC.
-
‘Epic’ LSU-Berkeley Book About Cybersecurity Hits Shelves This Fall
The authors discuss Cybersecurity in Context on the LSU blog.
General
Hardcover ISBN: 978-1-394-26244-1
eBook ISBN: 978-1-394-26245-8
The Table of Contents, Chapter 1, and Index are available for download here
The virtual machine (VM) requires a PC or Mac that can run VMWare Fusion. You will also need about 50 GB of free space for the VM
For Faculty
Digital evaluation copies are available here
Use the Wiley faculty site for access to the teacher’s manual, a model syllabus, and discussion prompts
For Self-Study Students
You can download our VM to study cybersecurity on your own
Bibtex
@book{cybersecurityincontext,
title = {Cybersecurity in Context},
author = {Chris Jay Hoofnagle and Golden R. Richard III},
url = {https://www.wiley.com/en-us/Cybersecurity+in+Context%3A+Technology%2C+Policy%2C+and+Law-p-9781394262441
https://cybersecurityincontext.com/},
isbn = {978-1-394-26244-1},
year = {2024},
publisher = {Wiley},
edition = {1st}
}